To establish a proper chain of custody, you carefully document every step from collection to storage, noting who handled the evidence, when, and where. Use tamper-evident containers and clearly label items with case details. Maintain secure storage and record all transfers and analysis activities. Follow strict protocols and employ forensic tools to preserve evidence integrity. If you want to understand the key practices that keep evidence legally sound, keep exploring the details.
Key Takeaways
- Maintain detailed logs of evidence collection, transfer, and storage with dates, times, personnel, and locations.
- Use tamper-evident containers and clear labeling to prevent contamination and ensure proper identification.
- Employ secure storage in locked, access-controlled environments to safeguard evidence integrity.
- Follow strict digital forensics procedures, including forensic imaging and write blockers, to preserve electronic data.
- Document every handling step and transfer to create an unbroken, transparent chain of custody record.

When handling evidence in a criminal investigation, maintaining a clear chain of custody is essential to guarantee its integrity and admissibility in court. This process isn’t just about documenting who has possession of evidence; it’s about ensuring that every step preserves its authenticity and prevents tampering or contamination. Digital forensics plays a key role here, especially when evidence includes electronic data like computers, smartphones, or servers. In such cases, you must follow strict procedures to avoid altering or corrupting digital evidence. Proper digital forensics techniques help you create a reliable record of every action taken, from seizure to analysis, which is fundamental for legal compliance. Furthermore, employing specialized forensic tools ensures data is handled correctly and securely. Legal compliance is at the core of establishing an unbreakable chain of custody. You need to adhere to established protocols and standards to guarantee your handling practices meet court requirements. Every transfer, storage, or analysis must be meticulously documented, including dates, times, locations, and the identities of those involved. This documentation creates an audit trail that proves the evidence has remained untouched or unaltered. When digital forensics experts are involved, they follow specialized procedures to maintain the integrity of electronic evidence, such as using write blockers to prevent data modification or copying evidence onto verified forensic images. These steps are essential to demonstrate that the evidence remains authentic and has not been compromised. It’s equally important to label and package evidence correctly. Use tamper-evident containers and mark them clearly with case numbers, collection dates, and the collector’s details. This prevents accidental or intentional contamination and makes it obvious if tampering occurs later. As you transfer evidence between locations or personnel, you must record each movement precisely, noting who handled it and under what circumstances. This ongoing documentation ensures transparency and accountability, which are fundamental for legal compliance. The chain of custody process also involves secure storage, where evidence should be kept in locked, access-controlled environments to prevent unauthorized access. In digital forensics, you should also maintain detailed logs of all analysis activities performed on electronic evidence. This includes documenting software tools used, procedures followed, and any copies or extractions made. Such thorough records bolster the credibility of your findings in court. Ultimately, by rigorously following these practices, you uphold the integrity of the evidence and support its admissibility, reinforcing the legal process. When you meticulously manage the chain of custody, you establish trust that the evidence presented is authentic, unaltered, and legally compliant, making your case stronger and more compelling in court.

BUT-N-LOC 32oz RPET Clear Hinged Lid Tamper Evident Container – 200 Pcs
MULTIPLE APPLICATIONS: These 32oz clear hinged plastic containers can easily fit many kinds of foods, such as fruits,…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Is Chain of Custody Different From Regular Evidence Handling?
You see, chain of custody differs from regular evidence handling because it emphasizes strict evidence tracking and custody documentation. You must carefully document every transfer, guaranteeing the evidence remains unaltered and secure. Unlike casual handling, this process requires detailed records of who has possession, when, and why. This rigorous approach helps maintain the integrity of the evidence and ensures it’s admissible in court.
What Are Common Mistakes That Compromise Evidence Integrity?
Like a fragile glass, evidence can easily break if you’re not careful. Common mistakes that compromise evidence integrity include evidence contamination from improper handling or storage, and improper documentation that leaves gaps in the chain. You might forget to seal evidence correctly or fail to log every transfer, which weakens the chain of custody. Stay vigilant, follow protocols precisely, and double-check your work to prevent these mistakes.
How Do Digital Evidence Chain of Custody Procedures Differ?
In digital forensics, your chain of custody procedures focus heavily on maintaining evidence integrity through strict documentation and secure handling. You verify digital evidence with hash values and logs, ensuring it hasn’t been been modified. Unlike physical evidence, you must also guarantee proper digital evidence preservation, such as using write-blockers. This process emphasizes evidence verification at every stage, preventing tampering and supporting admissibility in court.
Can Chain of Custody Be Maintained if Evidence Is Transferred Internationally?
Yes, you can maintain chain of custody during an international transfer if you carefully document each step, ensuring legal compliance. You must follow proper procedures, such as securing evidence in tamper-evident packaging, recording all transfers with detailed logs, and complying with both local and international laws. Clear documentation and communication with involved authorities help preserve the integrity of the evidence throughout the international transfer process.
What Training Is Required for Personnel Handling Evidence?
You need specialized training in evidence preservation and security protocols to handle evidence properly. This training covers proper collection, documentation, packaging, and storage techniques to prevent contamination or loss. You’ll also learn how to maintain a secure chain of custody, ensuring that evidence remains admissible in court. Regular refreshers and updates on best practices help you stay compliant with legal standards and protect the integrity of the evidence throughout its handling.

WiebeTech FCDv6 Forensic ComboDock Hard Drive Write Blocker
Digital and forensics investigators
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
Remember, the chain of custody is the key that locks the integrity of your evidence. Like a delicate chain links a sturdy anchor, each step holds the weight of truth and justice. If one link weakens, the entire chain risks breaking, casting doubt on your case. Keep it secure, keep it clear—because in the end, your careful handling is what preserves the beacon of truth shining through the darkness of doubt.
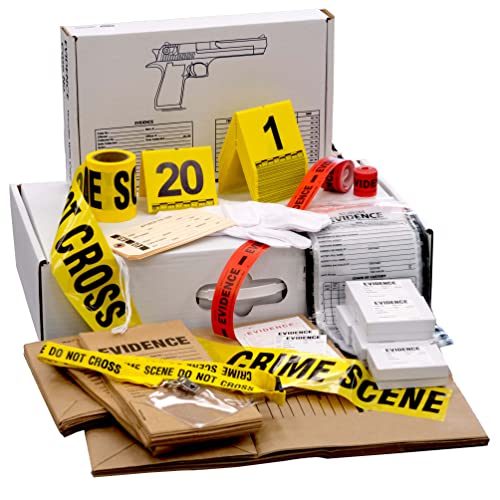
Crime Scene Forensic Supply Kit for Classrooms – Evidence Bags – Tents – Tape – Labels
Over 50 paper and plastic evidence bags, assorted sizes.
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Vaultz Storage Lock Box – 6.5 x 19.25 x 13.5 Inch Lockable Dorm Storage Trunk with Combination Lock – Briefcase, Medicine Box, Lock Boxes for Personal Items, Cash, Laptop – Black on Black
STORE VALUABLES – Our lockable storage box is ideal for documents, money, wallets, cash, passports, electronics, keys, and…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.









